New Lead2pass Cisco 350-018 Practice Test Free Download (685-695)
2016 July Cisco Official New Released 350-018 Q&As in Lead2pass.com!
100% Free Download! 100% Pass Guaranteed!
Cisco 350-018 exam is very popular in Cisco field, many Cisco candidates choose this exam to add their credentials. There are many resource online to offering Cisco 350-018 exam questions, through many good feedbacks, we conclude that Lead2pass can help you pass your test easily with Cisco 350-018 exam questions. Choose Lead2pass to get your Cisco 350-018 certification.
Following questions and answers are all new published by Cisco Official Exam Center: http://www.lead2pass.com/350-018.html
QUESTION 685
What protocol is responsible for issuing certificates?
A. SCEP
B. AH
C. GET
D. ESP
E. DTLS
Answer: A
QUESTION 686
Refer to the exhibit. Which statement about the effect of this command is true? 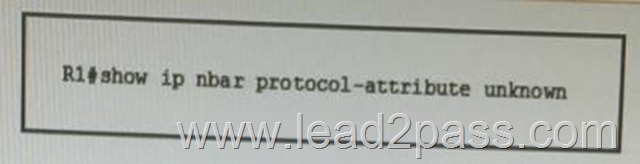
A. It lists the current protocol-to-port mappings of NBAR.
B. It lists traffic that is packet switched and bypassed by NBAR.
C. It lists the number of packets processed for unknown and unclassified flows.
D. It lists the attributes configured for unknown and unclassified flows.
E. It displays the link age for unknown and unclassified flows.
Answer: D
QUESTION 687
Which four of these attacks or wireless tools can the standard IDS signatures on a wireless LAN controller detect? (Choose four.)
A. long HTTP request
B. SYN flood
C. Deauthorization flood
D. NetStumbler
E. Wellenreiter
F. Association flood
G. AirSnort
H. Fragment Overlap attack
Answer: CDEG
QUESTION 688
What Cisco IOS feature prevents an attacker from filling up the MTU cache for locally generated traffic when using path MTU discovery?
A. Use NetFlow information to export data to a workstation.
B. Force all traffic to send 1280-byte Packets by hard coding the MSS.
C. Enable flow-label marking to track packet destination.
D. Enable flow-label switching to track IPv6 packets in the MPLS cloud.
E. Always use packets of 1500-byte size or larger.
Answer: C
QUESTION 689
What technology can you implement on your network to allow Independent applications to work with IPv6-capable applications?
A. DS-Lite
B. NAT-PT
C. ISATAP
D. NAT 6to4
E. NAT64
Answer: E
QUESTION 690
Which three of these statements about a zone-based policy firewall are correct? (Choose three.)
A. An interface can be assigned to only one security zone.
B. By default, all traffic to and from an interface that belongs to a security zone is dropped unless explicitly allowed in the zone-pair policy.
C. Firewall policies, such as the past, inspect, and drop actions, can only be applied between two zones.
D. In order to pass traffic between two interfaces that belong to the same security zone, you must configure a pass action using class-default.
E. Traffic cannot flow between a zone member interface and any interface that is not a zone member.
Answer: ACE
QUESTION 691
Refer to the exhibit. What is the maximum number of hops from the device that generated the given output to its BGP neighbor at 4.4.4.4? 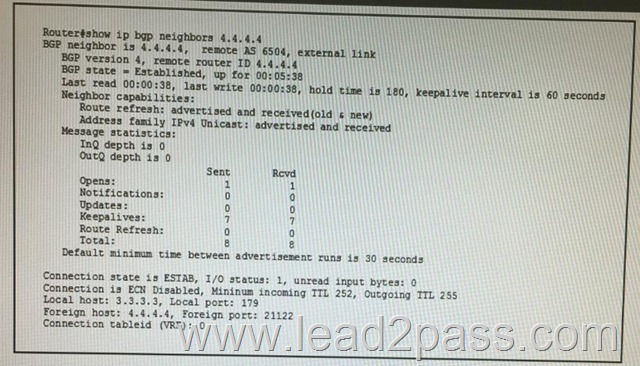
A. 3
B. 252
C. 5
D. 255
E. 2
F. 254
Answer: A
QUESTION 692
Which two statements about 802.1x authentication with port security are true? (Choose two.)
A. If any client causes a security violation, the port is immediately placed in spanning-tree disabled mode.
B. An entry is created in the secure host table for any client that is authenticated and manually configured for port security, even if the table is full.
C. 802.1x manages network access for all authorized MAC addresses.
D. If a client is authenticated and the port security table is full, the oldest client is aged out.
E. If any host causes a security violation, the port is immediately error-disabled.
Answer: BE
QUESTION 693
Refer to the exhibit.Which as-path access-list regular expression should be applied on R2 as a neighbor filter list to only allow updates with an origin of AS 65503?
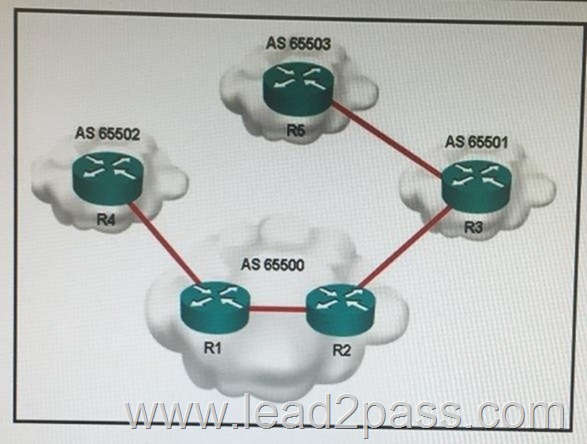
A. _65503.?$
B. ^65503 .*
C. 65503
D. _65503_
E. _65503$
F. ^65503$
Answer: B
QUESTION 694
If an ASA device is configured as a remote access IPsec server with RADIUS authentication and password management enabled, which type of authentication will it use?
A. MS-CHAFV2
B. MS-CHAPv1
C. RSA
D. NTLM
E. PAP
Answer: E
QUESTION 695
Drag and drop the step in the Cisco ASA packet processing flow on the left into the correct order of operations on the right. 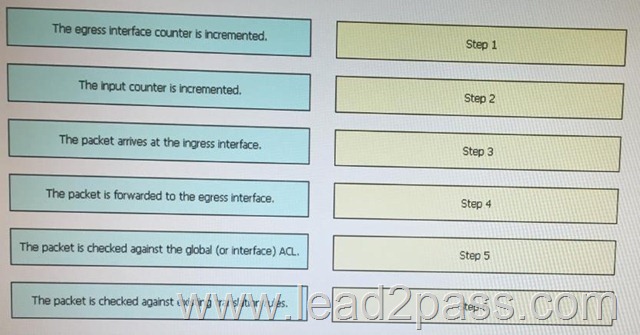
Answer: 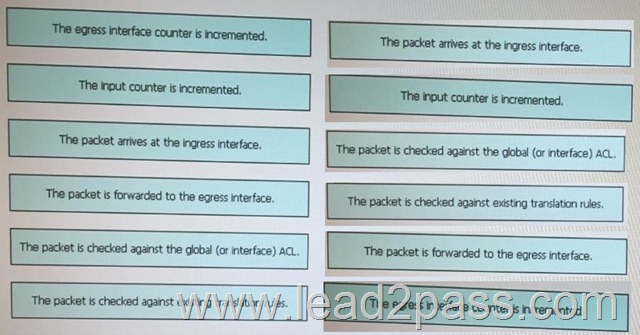
Cisco 350-018 exam questions are available in PDF and VCE format. This makes it very convenient for you to follow the course and study the exam whenever and wherever you want. The Cisco 350-018 exam questions follow the exact paper pattern and question type of the actual 350-018 certification exam, it lets you recreate the exact exam scenario, so you are armed with the correct information for the 350-018 certification exam.
2016 Cisco 350-018 exam dumps (All 788 Q&As) from Lead2pass:
http://www.lead2pass.com/350-018.html [100% Exam Pass Guaranteed]